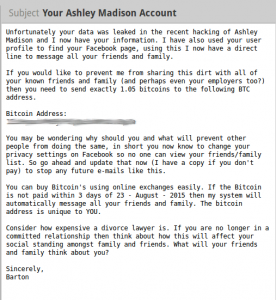
It was bound to happen: someone decided to blackmail members of online affairs website Ashley Madison, whose entire database was leaked earlier this week by a group calling themselves the "Impact Team". Shortly thereafter, an unknown group or individual has been sending extortion emails demanding Bitcoin for silence:
Of those who had accounts on the cheating website, we asked ourselves: how many are actually paying the blackmailers? Does such a campaign work at all?
To begin our investigation, we noted that the addresses in our samples were all different and freshly generated, meaning it had no previous activity on the Bitcoin blockchain we could trace. (Bitcoin addresses are merely an encoded version of randomly generated cryptographic keys, and thus generating new addresses is free and easy. In fact, most modern Bitcoin wallet software generates a new addresses for every incoming transaction, effectively making them ephemeral in use).
However, we realized that all the emails consistently demanded "exactly 1.05" Bitcoins from their victims, suggesting that we could search the blockchain for transactions paying that amount to infer if such extortions were being paid.
Specifically,
we found 67 suspicious transactions totalling 70.35 BTC or approximately 15814 USD within the extortion time frame of approximately 4 days paying 1.05 BTC to addresses, with no previous activity, and with 2 or fewer transaction outputs. All suspicious address we found are attached below. (We conservatively restricted ourselves to ordinary transactions with 2 or less outputs, thus excluding those which were less likely to be simple one-to-one payments.)
To put this in perspective, in the three months prior to 8/22/2015 when we first started seeing the extortion emails, we saw transactions matching the above pattern at a rate of approximately 5.3 per 100,000 transactions, versus 8.9 during the extortion period.
We can strongly reject the null hypothesis that the incidence of matching transactions during the extortion period followed a Poisson distribution at the historical rate, thus allowing us to infer that perhaps the 40% of the 67 transactions totaling approximately
6400 USD may be attributable to victims paying the blackmail.
So, although we cannot say anything conclusively, we have found out that:
1. For a spammer with pre-existing infrastructure and tools, this extortion campaign could have yielded a worthwhile sum for very little effort. All the blackmailer had to do was download the Ashley Madison data, extract the email addresses, generate a Bitcoin address for each victim and send out the emails.
2. Since this search would not have been possible without the consistent extortion amount, we suspect that future attempts at Bitcoin-based blackmail will randomize the amount they demand.
In order to go deeper into this analysis, the next step would be to follow the trail of Bitcoins leading to each suspicious address to see if they are connected on the blockchain to each other or any other known suspicious addresses. Such analysis could potentially help law enforcement to deanonymize and pursue the perpetrators.
1DriJgHZrYYmY4jRiVQaKHzcJpUjCpGeUQ
15Z8ouMiGi8mkzramRS8w2r5rTc6vmKmtJ
1FS273GrqQeDgHiFUQhmcVcdDsRxP8bH37
141bvr3GG4L5vaMEB1jNRQRxUVs8SL2Ues
1KktFva2VvC7ccJiLcRphziFejqLsAm19L
13qcYDvm3KJgQs8oLNDDmCRSUVNdFk1U7u
1NFA7wdpAnd98WNXSy14XFpWJvPFDMqWdB
13mTQa1Lu7PY7YQ9i1kHfJ2LAQPSHzipPC
13UhYXexu4gMZV7wuF6nMvcoskpZTzndFc
1LsAnYbqx1M3aVAxAx4HQ2s4mVmtTpbENH
18rAWeapsa8eYSPzLW7LLt5RPjaG99RyLU
1A1tD6Eh575B65FBnCU3nFyiE6F8XSTnGn
1PXmkZY5Dfdd21HnTsswYqA5ofBGA4uKCe
13bSLj3Meieo9c88hzUZZ7JCUDjyPFoPJW
1BcrFesya4yMMNt38SCkBWUS7cfeXWNfaZ
163xg99azNdRPysSSiKppbzsAeY8CZfNB4
137oYdzJkZ34Ragqv4mXr9b2GtmyTCKFdn
129DGouYdepTaoyPCoPno6XPBUdVqYLJzc
14ckjPngaCQ6TPXSJdajj2JbNKb1Mdb4wY
1C9w3DrL4Y4aJbf56adEPrbGYSzqrQshao
1LfbeLAcafgi4Dsgi6kZYutp8zco2Uhbty
1KBKxi9npjjaAFBb8D7VoFk65PVFJTfNFE
1ErwF3T6QCdZ75PBXZdyxXJPN2k7bBV9fd
1Nr2y7XD8c27tMQF5XrQJdfUWjCZ3zY5uy
3HjnsddWrsJGzCixWebUbWPvhQBnqmNKuS
1CHgfsytZX5sxYWmoTW9CLtRenALa438ZB
1P5Jz8MkEHrLvkst4nE3obENFk49h1naks
17N2PbooaR4F3C6DWkq2KwLubWGvZRgL7X
12nqFiUh78NnUWWWPDYoi77Wxu2jjzYqZu
1NTq99ERynPeW4tD66dU11rzg1srmLDS4z
1G52wBtL51GwkUdyJNYvMpiXtqaGkTLrMv
18euqRRpC2Zp9i9dwrT7Qp3M8jfbu9TUn6
1Q3AvrmZ8cykHGQ7kCkSZaopnWiHPzc1Qw
1y6W32cJfsRW5c16SUEXSyexWpvMbsBxn
1BkUNiTfJRTTG1iycaWGZavmLnLVHorUUo
1JjEY8H6QmwKYXuusksqCta2WhVQQG5e59
1CD3BoUwRC5uPxZSVeHhNGKcrv7iwddVbY
1MaqCVfiidjLitysy3vbWrJ12rU1xvEdyD
1B5NT9jV7BXoSPdEcbcCUAcPrpF7WeBLCc
17TmBnHmnkoQboVCmrcJGT2WzkBY8KRw6F
1JFf9QN9iNJA9QFhncEM5FGxqbr1JUmPP8
16w9fAaX8HEh4CMYAqdi9YvP93CSthV1jz
1LnxsZDPNkU96mrYoS1CQwxPmrhJyrgujM
1HZErPx5XPrp8mH98rKRjyazQLYN7j34Lk
14YeaK34GE68S6YASdtHR1iThj8c8hBQ1C
1PUt7bm1ZU6BRT85yDJxd651Fgneveuzs3
17CcixA4fyEmscXPsZRshecXzJ52eoKNNY
14gkHySfCnoV4Fy4nCxoLUgavMP3DMXKsS
1Gscvx3ugexW4xKjBFogQtQRsHR9Eh8v4n
1ETmDWjyto3gGegqch41PCeYJiVx9pmsuv
1EuRpZCEoyRKWcEpv6jD42N2CxJWrrETcD
1MAwvr21q95UBu6y4WhRM47K5RBijQ164G
1Kbj3tzAbtHgJHt6h6G5PuvWYRZkWXAfhH
1KFc1tekeQtZg48pKbCEU2j7J14N2XFTNW
1Hmjw6JcNDxCQuVo7pkUmRmJzRJe4yLze9
13Mj4nmV127symEJ6GTTb4kdTWyQ884QoN
12bbs3MZAsd9mseXKTA93PtHVd2nSkvjDy
137ENC6fNM97tawPMAGgyn9BKLEmkTx7Xd
1JBygewRQuHuh4qJnpQtb1qCfwNJ2zNrg5
1KbhhzTu14XPSMbBPCxEX4o3kTL9QS2UhZ
1Fb4zhTg4a7zmdRWJAJ1cg9A5pZSMdGGeA
19UMZViRQShqJz49cDDEiz3P1Steitze8A
1DUscKj5QoBoYAXq8cLa8bF8f4x9fNxSPx
1DG19BHaTWbLvaSXjGCmc8HmmptSoZSjVH
1HbUkTKH46RY9UBByUrW1qKNAXeCAqJi8E
1PCY5o15oeugfF9NcF3XiL776Bg4sSC9KL
12NXrKmp68vL59oh5Q1aMqNs35CBC97M1q